Appearance
Policy Packs
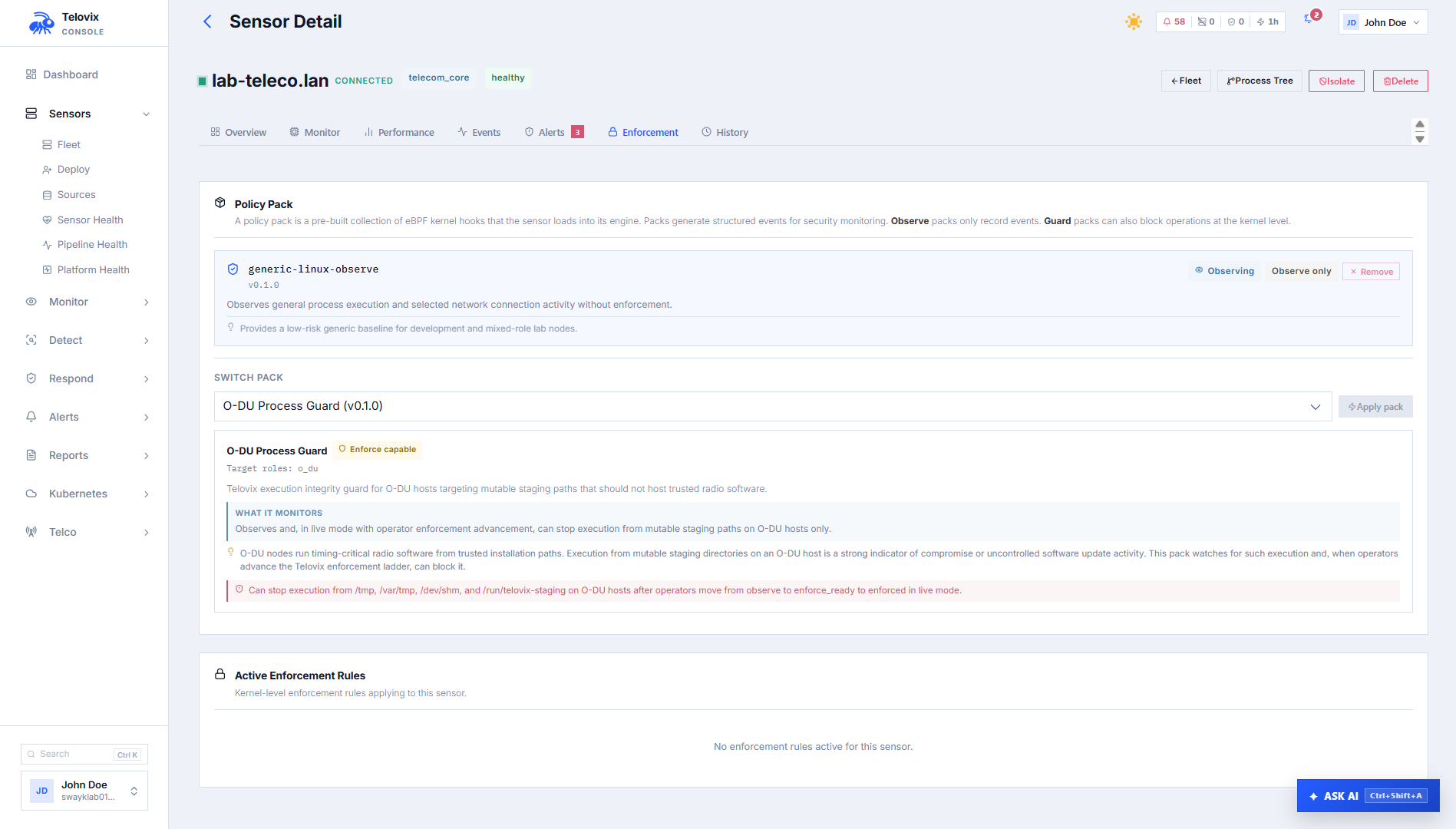
Policy packs are curated collections of detection and enforcement rules distributed to sensors through the Console. Each pack targets specific node roles, protocol families, and operational assumptions. The sensor applies the assigned pack within one heartbeat cycle (15 seconds) and verifies each policy file's Ed25519 signature before loading it.
How packs work
- An operator assigns a pack version to a sensor or group of sensors from the Console.
- The assignment is stored in the Console database and included in the next heartbeat response for each affected sensor.
- The sensor receives the pack assignment, downloads and caches the TracingPolicy YAML files locally under
compiled-policies/{pack_id}/{version}/, and applies each file to the embedded eBPF engine via gRPC. - Each
.yamlfile is accompanied by a.yaml.sigsidecar. The sensor verifies the Ed25519 signature against thepolicy-signing.pubkey it received at enrollment before loading the policy. Policies with invalid signatures are rejected. - The current assignment is persisted to
assigned-pack.jsonso it survives a sensor restart. - Enforcement state (
observe,enforce_ready,enforced) is part of the assignment and delivered the same way.
Pack catalog
The Telovix Console serves the pack catalog from the policy pack directory configured during initial setup. Each pack lives in a subdirectory named {pack_id}/{version}/ and contains a manifest.json and an engine-input.json.
The following packs are included with the standard installation. All are at version 0.1.0 in the current release.
O-DU packs
| Pack ID | Title | Kind | Target roles |
|---|---|---|---|
o-du-baseline-observe | O-DU Baseline Observe | observe | o_du |
o-du-fronthaul-observe | O-DU Fronthaul Observe | observe | o_du |
o-du-process-guard | O-DU Process Guard | guard | o_du |
o-du-process-guard is enforcement-capable. When operators advance the enforcement ladder to enforced, it can block execution from /tmp, /var/tmp, /dev/shm, and /run/telovix-staging on O-DU hosts.
O-CU packs
| Pack ID | Title | Kind | Target roles |
|---|---|---|---|
o-cu-baseline-observe | O-CU Baseline Observe | observe | o_cu |
o-cu-core-signaling-observe | O-CU Core Signaling Observe | observe | o_cu |
o-cu-ims-session-observe | O-CU IMS Session Observe | observe | o_cu |
o-cu-signaling-observe | O-CU Signaling Observe | observe | o_cu |
O-Cloud packs
| Pack ID | Title | Kind | Target roles |
|---|---|---|---|
o-cloud-baseline-observe | O-Cloud Baseline Observe | observe | o_cloud |
o-cloud-core-observe | O-Cloud Core Observe | observe | o_cloud |
o-cloud-integrity-guard | O-Cloud Integrity Guard | guard | o_cloud |
o-cloud-interconnect-observe | O-Cloud Interconnect Observe | observe | o_cloud |
o-cloud-runtime-drift-observe | O-Cloud Runtime Drift Observe | observe | o_cloud |
o-cloud-integrity-guard is enforcement-capable. When advanced to enforced, it can block execution from /tmp, /var/tmp, /dev/shm, and /run/telovix-staging on O-Cloud hosts.
General
| Pack ID | Title | Kind | Target roles | Support level |
|---|---|---|---|---|
generic-linux-observe | Generic Linux Observe | observe | generic_linux, o_du, o_cu | development |
::: note The generic-linux-observe pack has support_level: development. It is intended for lab and development environments, not production deployments. :::
Pack manifest fields
Each manifest.json defines the following fields:
| Field | Description |
|---|---|
pack_id | Unique identifier used in file paths and Console display |
pack_version | SemVer string |
pack_family | Logical grouping (e.g. telecom_baseline, telecom_du_integrity) |
target_roles | Node roles this pack is intended for |
protocol_families | Protocol families covered (e.g. 5g_nr_ran, 5g_core_signaling) |
pack_kind | observe (detection only) or guard (enforcement-capable) |
title | Human-readable name shown in the Console |
description | What the pack monitors |
rationale | Why the pack exists and what threat it addresses |
scope_summary | Exact scope of collection |
observation_class | Types of activity observed (e.g. process_execution network_activity) |
telecom_context | Telecom-specific context shown in the Console |
support_level | official or development |
enforcement_capable | true if this pack can be advanced past observe |
enforcement_summary | Description of what enforcement does (only present when enforcement_capable: true) |
Role assignment is validated: a pack's target_roles must include the sensor's declared_role or generic_linux. Assigning a pack targeting o_du to a sensor declared as amf returns a RoleMismatch error.
Provenance states
When you configure a pack registry URL in Console Settings, the Console verifies pack integrity against the registry before assignment. Without a registry, the Console serves packs from local disk without remote verification.
| State | Meaning |
|---|---|
verified | Pack manifest signature verified against registry using Ed25519 |
unverified | Registry not configured; pack loaded from local disk without remote verification |
mismatch | Pack manifest does not match the registry record |
unavailable | Registry configured but unreachable or key not found |
local_custom | Pack marked as a local custom pack; no provenance check performed |
Assigning a pack
Single sensor
In the Console, go to Sensors, select a sensor, and click Assign Pack. Choose the pack ID and version from the catalog.
Kubernetes namespace scope
For Kubernetes-deployed sensors, you can limit policy application to specific namespaces. In the Console, go to Sensors > [sensor] > Assign Pack and enter the namespace scope (e.g. 5g-core, ran-workloads) in the namespace filter field.
When a namespace scope is set, the sensor applies the pack rules only to events from pods in the specified namespaces.
Fleet assignment
In the Console, go to Sensors > Fleet Actions > Assign Pack to assign a pack to multiple sensors at once. The Console shows a preflight summary of outcomes for each sensor (ready, assigned, blocked, failed) before you confirm. A sensor is blocked from assignment if its declared role does not match the pack's target_roles.
Manage enforcement states
Every pack assignment has an enforcement state. The state can only advance forward one step at a time, and only for packs with enforcement_capable: true.
observe - enforce_ready - enforcedReturning to observe is always allowed from any state.
| State | Behavior |
|---|---|
observe | Events are recorded and alerts are generated. No blocking. Default for all new assignments. |
enforce_ready | Pack is loaded in enforcement mode; the sensor is ready to enforce but has not yet entered the enforced state. Used as a final review gate before enforcement. The sensor must be in runtime_mode: live. |
enforced | Active blocking is enabled. Only available after enforce_ready and only for enforcement-capable packs. |
In the Console, go to Sensors > [sensor] > Enforcement to advance the enforcement state. Before advancing to enforce_ready or enforced, review the enforcement verification panel on the same page, which shows the readiness class (NotReady, ReviewRequired, or CandidateForEnforceReady), the list of blocking conditions, and any caution conditions.
List and inspect the catalog
In the Console, go to Policies > Policy Packs to view all packs in the catalog with their provenance state. Select a sensor from Sensors to see its current pack assignment.
Verify policy signatures
Each policy YAML file in a pack has a .yaml.sig sidecar containing an Ed25519 signature over the message:
telovix-policy-v1:{policy_name}\n{yaml_content}The sensor verifies this signature against the policy-signing.pub key it received at enrollment. Policies with invalid signatures are rejected and the assignment fails. This protects against tampering with policy files that cross a network or storage boundary.
If no .sig sidecar exists but a signing key is configured, the sensor logs a warning and loads the policy anyway for backwards compatibility with pre-signing pack versions.
Troubleshooting
Pack assignment returns RoleMismatch
The sensor's declared_role is not listed in the pack's target_roles. Use a pack that targets the sensor's declared role, or correct the declared role on the sensor to match the intended pack.
Pack assignment returns PackRootNotConfigured
The policy pack directory has not been configured in the Console. Set the policy pack directory path in Console Settings and restart the Console before attempting assignment again.
Pack shows provenance_state: unavailable
A pack registry URL is configured in Console Settings but the registry is currently unreachable. Check the registry URL and network connectivity from the Console host. Packs continue to work from local disk, but the mismatch state persists until the registry is reachable.
Pack not appearing in sensor events after assignment
Policy signature verification failed on the sensor, or the heartbeat carrying the assignment has not yet been delivered. Check the sensor logs with journalctl -u telovix-sensor -n 50 --no-pager | grep policy and verify that policy-signing.pub is present in the sensor state directory (default /var/lib/telovix-sensor/).
enforce_ready transition rejected
The sensor is not in live runtime mode, or the trust health is not healthy. Review the enforcement verification panel on the sensor enforcement page for the specific blocking conditions preventing the transition.